Crossover ideas for writing, gaming, and general amusement. All creations mentioned are copyright(c), trademarked(tm) and soforth their individual owners. No infringement on existing copyright is intended. Not responsible whatsoever for the results or any reactions they cause.
Tutorial
Status: Deprecated
This article covers a version of Ubuntu that is no longer supported. If you are currently operate a server running Ubuntu 12.04, we highly recommend upgrading or migrating to a supported version of Ubuntu:
- Upgrade to Ubuntu 14.04.
Reason:Ubuntu 12.04 reached end of life (EOL) on April 28, 2017 and no longer receives security patches or updates. This guide is no longer maintained.
See Instead:
This guide might still be useful as a reference, but may not work on other Ubuntu releases. If available, we strongly recommend using a guide written for the version of Ubuntu you are using. You can use the search functionality at the top of the page to find a more recent version.
Introduction
- It cracked open the door with a cross-play beta for Fortnite a little over a year ago, and now it's allowing all developers to make use of cross-platform capabilities.
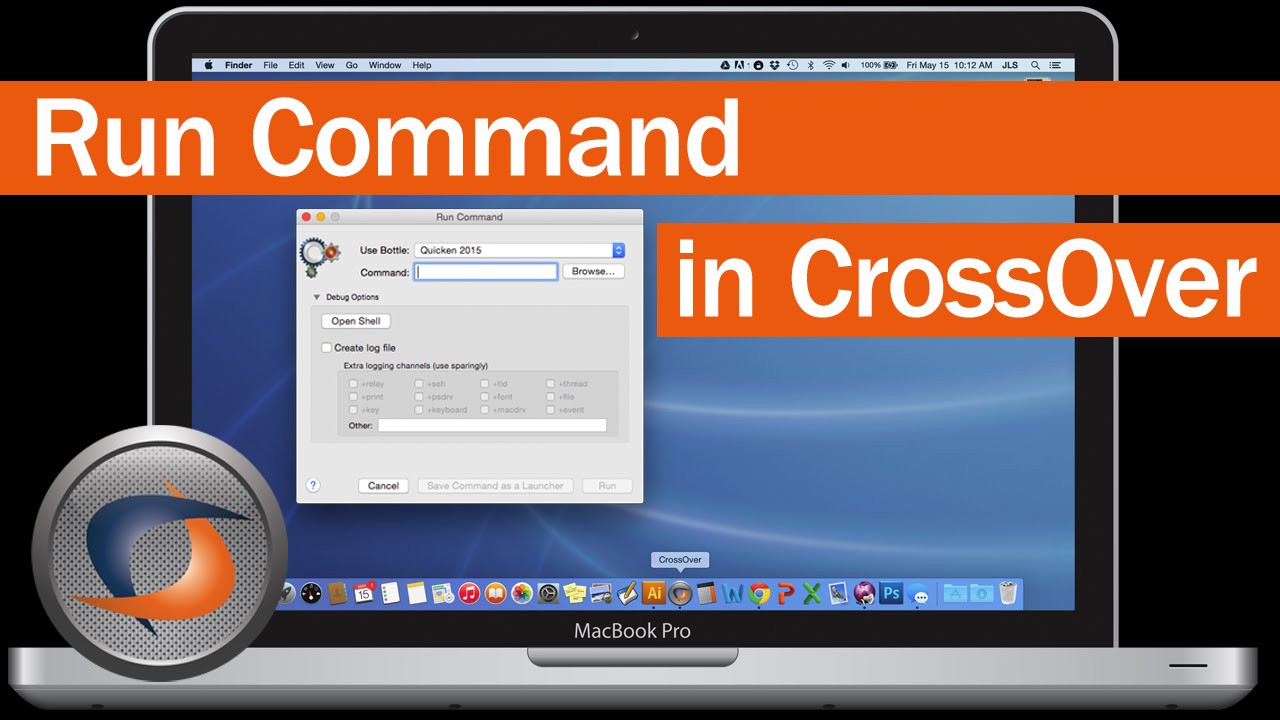
- CrossOver can see any external hard drives (USB and FireWire) and memory sticks that OS X can see, and you’ll have access to them from the Open and Save dialog boxes in Windows.
- How to Open Exe Files on Mac. This wikiHow teaches you how to run Windows' executable (EXE) files on a Mac. To do so, you can either install WINE, which is free software, or install Windows 8 or 10 using your Mac's Boot Camp feature.
PostreSQL, or postgres, is a popular database management system that can organize and manage the data associated with websites or applications. Replication is a means of copying database information to a second system in order to create high availability and redundancy.
There are many ways to set up replication on a postgres system. In this tutorial, we will cover how to configure replication using a hot standby, which has the advantage of being relatively simple to configure.
To do this, we will need two Ubuntu 12.04 VPS instances. One will serve as the master database server and the other will function as a slave, which will replicate.
Install PostgreSQL Software
The steps in this section should be performed on both the master and slave servers.
The postgres software is available in Ubuntu’s default repositories. Install the appropriate packages with these commands.
PostgreSQL creates a user called “postgres” in order to handle its initial databases. We will configure ssh access between our servers to make transferring files easier.
We will need to set a password for the postgres user so that we can transfer the key files initially. If you desire, you can remove the password at a later time:
Switch over to the postgres user like this:
Generate an ssh key for the postgres user:
Press “ENTER” to all of the prompts that follow.
Transfer the keys to the other server by typing:
<pre>
ssh-copy-id <span class=“highlight”>IPaddressofoppositeserver</span>
</pre>
You should now be able to ssh freely between your two servers as the postgres user.
Configure the Master Server
We will begin by configuring our master server. All of these commands should be executed with the postgres user.
First, we will create a user called “rep” that can be used solely for replication:
<pre>
psql -c “CREATE USER rep REPLICATION LOGIN CONNECTION LIMIT 1 ENCRYPTED PASSWORD ’<spanhighlight”>IPaddressof_slave</span>/32 md5
</pre>
Save and close the file.
Next, we will open the main postgres configuration file:
Find these parameters. Uncomment them if they are commented, and modify the values according to what we have listed below:
<pre>
listenaddresses = ‘localhost,<span class=“highlight”>IPaddressofTHIShost</span>’
wallevel = 'hotstandby’
archivemode = on
archivecommand = 'cd .’
maxwalsenders = 1
hotstandby = on
</pre>
Save and close the file.
Restart the master server to implement your changes:
Configure the Slave Server
Begin on the slave server by shutting down the postgres database software:
We will be making some similar configuration changes to postgres files, so change to the configuration directory:
Adjust the access file to allow the other server to connect to this. This is in case we need to turn the slave into the master later on down the road.
Again, add this line somewhere not at the end of the file:
<pre>
host replication rep <span class=“highlight”>IPaddressof_master</span>/32 md5
</pre>
Save and close the file.
Next, open the postgres configuration file:
You can use the same configuration options you set for the master server, modifying only the IP address to reflect the slave server’s address:
<pre>
listenaddresses = 'localhost,<span class=“highlight”>IPaddressofTHIShost</span>’
wallevel = 'hotstandby’
archivemode = on
archivecommand = 'cd .’
maxwalsenders = 1
hotstandby = on
</pre>
Save and close the file.
Replicating the Initial database:
Before the slave can replicate the master, we need to give it the initial database to build off of. This is because it reads the logs off of the master server and applies the changes to its own database. We need that database to match the master database.
On the master server, we can use an internal postgres backup start command to create a backup label command. We then will transfer the database data to our slave and then issue an internal backup stop command to clean up:
<pre>
psql -c “select pgstartbackup('initialbackup’);”
rsync -cva –inplace –exclude=*pgxlog* /var/lib/postgresql/9.1/main/ <span class=“highlight”>slaveIPaddress</span>:/var/lib/postgresql/9.1/main/
psql -c “select pgstopbackup();”
</pre>
The rsync command may have had an error on modifying the certificate files, but this is okay for our use. The master’s data should now be on the slave.
We now have to configure a recovery file on our slave. On the slave navigate to the data directory:
Here, we need to create a recovery file called recovery.conf: El diablo ilustrado descargar pdf gratis.
Fill in the following information. Make sure to change the IP address of your master server and the password for the rep user you created:
<pre>
standbymode = 'on’
primaryconninfo = 'host=<span class=“highlight”>masterIPaddress</span> port=5432 user=rep password=<span class=“highlight”>yourpassword</span>’
trigger_file = ’/tmp/postgresql.trigger.5432’
</pre>
The last line in the file, trigger_file, is one of the most interesting parts of the entire configuration. If you create a file at that location on your slave machine, your slave will reconfigure itself to act as a master.
This will break your current replication, especially if the master server is still running, but is what you would need to do if your master server goes down. This will allow the slave to begin accepting writes. You can then fix the master server and turn that into the slave.
You should now have the pieces in place to start your slave server. Type:
You’ll want to check the logs to see if there are any problems. They are located on both machines here:
You should see that it is successfully connecting to the master server.
Test the Replication
We will see first-hand if our servers are replicating correctly by making some changes on the master server and then querying the slave.
On the master server, as the postgres user, log into the postgres system by typing:
Your prompt will change to indicate that you are now communicating with the database software.
We will create a test table to create some changes:
Now, we can insert some values into the table with the following commands:
You can now exit out of this interface by typing:
Now, on the slave, enter the database interface in the same way:
Now, we can see if the data we entered in the master database has been replicated on the slave:
Excellent! Our data has been written to both the master and slave servers.
Let’s see if we can insert more data into the table on our slave:
As you can see, we are unable to insert data into the slave. This is because the data is only being transferred in one direction. In order to keep the databases consistent, postgres must make the slave read-only.
Conclusion
You should now have a master and slave PostgreSQL server configured to communicate effectively. If you have an application that will be writing to and querying the databases, you could set up a load balancing scheme to always write to the master, but split the reads between the master and slave. This could increase the performance of your database interactions.
<div class=“author”>By Justin Ellingwood</div>
Name
ssh-keygen - authentication key generation, management and conversion
Synopsis
ssh-keygen [-q] [-bbits] -ttype [-Nnew_passphrase] [-Ccomment] [-foutput_keyfile]
ssh-keygen -p [-Pold_passphrase] [-Nnew_passphrase] [-fkeyfile]
ssh-keygen -i [-finput_keyfile]
ssh-keygen -e [-finput_keyfile]

ssh-keygen -y [-finput_keyfile]
ssh-keygen -c [-Ppassphrase] [-Ccomment] [-fkeyfile]
ssh-keygen -l [-finput_keyfile]
ssh-keygen -B [-finput_keyfile]
ssh-keygen -Dreader
ssh-keygen -Fhostname [-fknown_hosts_file] [-l]
ssh-keygen -H [-fknown_hosts_file]
ssh-keygen -Rhostname [-fknown_hosts_file]
ssh-keygen -Ureader [-finput_keyfile]
ssh-keygen -rhostname [-finput_keyfile] [-g]
ssh-keygen -Goutput_file [-v] [-bbits] [-Mmemory] [-Sstart_point]
ssh-keygen -Toutput_file-finput_file [-v] [-anum_trials] [-Wgenerator]
ssh-keygen [-n] [-Dsmartcard]
Description
ssh-keygen generates, manages and converts authentication keys for ssh(1). ssh-keygen can create RSA keys for use by SSH protocol version 1and RSA or DSA keys for use by SSH protocol version 2. The type of key to be generated is specified with the -t option. If invoked without anyarguments, ssh-keygen will generate an RSA key for use in SSH protocol 2 connections.
ssh-keygen is also used to generate groups for use in Diffie-Hellman group exchange (DH-GEX). See the MODULI GENERATION section for details.
Normally each user wishing to use SSH with RSA or DSA authentication runs this once to create the authentication key in ~/.ssh/identity,~/.ssh/id_dsa or ~/.ssh/id_rsa. Additionally, the system administrator may use this to generate host keys, as seen in /etc/rc.
Normally this program generates the key and asks for a file in which to store the private key. The public key is stored in a file with the same name but'.pub' appended. The program also asks for a passphrase. The passphrase may be empty to indicate no passphrase (host keys must have an empty passphrase), orit may be a string of arbitrary length. A passphrase is similar to a password, except it can be a phrase with a series of words, punctuation, numbers,whitespace, or any string of characters you want. Good passphrases are 10-30 characters long, are not simple sentences or otherwise easily guessable (Englishprose has only 1-2 bits of entropy per character, and provides very bad passphrases), and contain a mix of upper and lowercase letters, numbers, andnon-alphanumeric characters. The passphrase can be changed later by using the -p option.
There is no way to recover a lost passphrase. If the passphrase is lost or forgotten, a new key must be generated and copied to the corresponding public keyto other machines.
For RSA1 keys, there is also a comment field in the key file that is only for convenience to the user to help identify the key. The comment can tell whatthe key is for, or whatever is useful. The comment is initialized to 'user@host' when the key is created, but can be changed using the -c option.
After a key is generated, instructions below detail where the keys should be placed to be activated.
The options are as follows:
Specifies the number of primality tests to perform when screening DH-GEX candidates using the -T command.-B' Show the bubblebabble digest of specified private or public key file.
-bbits
Specifies the number of bits in the key to create. For RSA keys, the minimum size is 768 bits and the default is 2048 bits. Generally, 2048 bits is consideredsufficient. DSA keys must be exactly 1024 bits as specified by FIPS 186-2.
-Ccomment
Provides a new comment.
-c' Requests changing the comment in the private and public key files. This operation is only supported for RSA1 keys. The program will prompt forthe file containing the private keys, for the passphrase if the key has one, and for the new comment.
-Dreader
Download the RSA public key stored in the smartcard in reader.
-e' This option will read a private or public OpenSSH key file and print the key in RFC 4716 SSH Public Key File Format to stdout. This option allowsexporting keys for use by several commercial SSH implementations.
-Fhostname
Search for the specified hostname in a known_hosts file, listing any occurrences found. This option is useful to find hashed host names oraddresses and may also be used in conjunction with the -H option to print found keys in a hashed format.
-ffilename
Specifies the filename of the key file.
-Goutput_file
Generate candidate primes for DH-GEX. These primes must be screened for safety (using the -T option) before use.
-g' Use generic DNS format when printing fingerprint resource records using the -r command.
-H' Hash a known_hosts file. This replaces all hostnames and addresses with hashed representations within the specified file; the originalcontent is moved to a file with a .old suffix. These hashes may be used normally by ssh and sshd, but they do not reveal identifying informationshould the file's contents be disclosed. This option will not modify existing hashed hostnames and is therefore safe to use on files that mix hashed andnon-hashed names.
-i' This option will read an unencrypted private (or public) key file in SSH2-compatible format and print an OpenSSH compatible private (or public)key to stdout. ssh-keygen also reads the RFC 4716 SSH Public Key File Format. This option allows importing keys from several commercial SSHimplementations.
-l' Show fingerprint of specified public key file. Private RSA1 keys are also supported. For RSA and DSA keys ssh-keygen tries to find thematching public key file and prints its fingerprint. If combined with -v, an ASCII art representation of the key is supplied with the fingerprint.
-Mmemory
Specify the amount of memory to use (in megabytes) when generating candidate moduli for DH-GEX.
-n' Extract the public key from smartcard.
-Nnew_passphrase
Provides the new passphrase.
-Ppassphrase
Provides the (old) passphrase.
-p' Requests changing the passphrase of a private key file instead of creating a new private key. The program will prompt for the file containing theprivate key, for the old passphrase, and twice for the new passphrase.
-q' Silence ssh-keygen. Used by /etc/rc when creating a new key.
-Rhostname
Removes all keys belonging to hostname from a known_hosts file. This option is useful to delete hashed hosts (see the -H option above).
-rhostname
Print the SSHFP fingerprint resource record named hostname for the specified public key file.
-Sstart
Specify start point (in hex) when generating candidate moduli for DH-GEX.
-Toutput_file
Test DH group exchange candidate primes (generated using the -G option) for safety.
-ttype
Specifies the type of key to create. The possible values are 'rsa1' for protocol version 1 and 'rsa' or 'dsa' for protocol version 2.
-Ureader
Upload an existing RSA private key into the smartcard in reader.
-v' Verbose mode. Causes ssh-keygen to print debugging messages about its progress. This is helpful for debugging moduli generation. Multiple-v options increase the verbosity. The maximum is 3.
-Wgenerator
Specify desired generator when testing candidate moduli for DH-GEX.
-y' This option will read a private OpenSSH format file and print an OpenSSH public key to stdout.
Moduli Generation
ssh-keygen may be used to generate groups for the Diffie-Hellman Group Exchange (DH-GEX) protocol. Generating these groups is a two-step process:first, candidate primes are generated using a fast, but memory intensive process. These candidate primes are then tested for suitability (a CPU-intensiveprocess).
Generation of primes is performed using the -G option. The desired length of the primes may be specified by the -b option. Forexample:
- # ssh-keygen -T moduli-2048 -f moduli-2048.candidates
By default, each candidate will be subjected to 100 primality tests. This may be overridden using the -a option. The DH generator value will bechosen automatically for the prime under consideration. If a specific generator is desired, it may be requested using the -W option. Valid generatorvalues are 2, 3, and 5.
Screened DH groups may be installed in /etc/ssh/moduli. It is important that this file contains moduli of a range of bit lengths and that both endsof a connection share common moduli.
Files
Contains the protocol version 1 RSA authentication identity of the user. This file should not be readable by anyone but the user. It is possible to specifya passphrase when generating the key; that passphrase will be used to encrypt the private part of this file using 3DES. This file is not automatically accessedby ssh-keygen but it is offered as the default file for the private key. ssh(1) will read this file when a login attempt is made.~/.ssh/identity.pub
Contains the protocol version 1 RSA public key for authentication. The contents of this file should be added to ~/.ssh/authorized_keys on all machineswhere the user wishes to log in using RSA authentication. There is no need to keep the contents of this file secret.
~/.ssh/id_dsa
Contains the protocol version 2 DSA authentication identity of the user. This file should not be readable by anyone but the user. It is possible to specify apassphrase when generating the key; that passphrase will be used to encrypt the private part of this file using 3DES. This file is not automatically accessedby ssh-keygen but it is offered as the default file for the private key. ssh(1) will read this file when a login attempt is made.
~/.ssh/id_dsa.pub
Contains the protocol version 2 DSA public key for authentication. The contents of this file should be added to ~/.ssh/authorized_keys on all machineswhere the user wishes to log in using public key authentication. There is no need to keep the contents of this file secret.
~/.ssh/id_rsa
Contains the protocol version 2 RSA authentication identity of the user. This file should not be readable by anyone but the user. It is possible to specify apassphrase when generating the key; that passphrase will be used to encrypt the private part of this file using 3DES. This file is not automatically accessedby ssh-keygen but it is offered as the default file for the private key. ssh(1) will read this file when a login attempt is made.

~/.ssh/id_rsa.pub
Contains the protocol version 2 RSA public key for authentication. The contents of this file should be added to ~/.ssh/authorized_keys on all machineswhere the user wishes to log in using public key authentication. There is no need to keep the contents of this file secret.
/etc/ssh/moduli
Contains Diffie-Hellman groups used for DH-GEX. The file format is described in moduli(5).
Environment
The reseeding of the OpenSSL random generator is usually done from /dev/urandom. If the SSH_USE_STRONG_RNG environment variable is set tovalue other than 0 the OpenSSL random generator is reseeded from /dev/random. The number of bytes read is defined by the SSH_USE_STRONG_RNGvalue. Minimum is 6 bytes. This setting is not recommended on the computers without the hardware random generator because insufficient entropy causes theconnection to be blocked until enough entropy is available.See Also
ssh(1), ssh-add(1), ssh-agent(1), moduli(5), sshd(8)
Authors
OpenSSH is a derivative of the original and free ssh 1.2.12 release by Tatu Ylonen. Aaron Campbell, Bob Beck, Markus Friedl, Niels Provos, Theo de Raadt andDug Song removed many bugs, re-added newer features and created OpenSSH. Markus Friedl contributed the support for SSH protocol versions 1.5 and 2.0.
BSD April 14, 2013 BSD
Referenced By
amaddclientHow To Use Keygen Crack
(8),autossh(1),backup-manager(8),gsimoduli(5),gsissh(1),gsissh-keysign(8),gsissh_config(5),gsisshd(8),rsnapshot(1),scp(1),sftp(1),ssh-keysign(8),ssh_config(5),How To Open Keygen File
tlsa(1)